This article was originally published by Alyssa Rosezweig under the CC BY-SA 4.0 license.
I refuse to carry a cellphone – to my puzzled friends in our techno-obsessed society, here’s why. A number of you have already asked what my number is to text me. Perhaps you were a teacher in one of my classes asking me to run some proprietary software in class. Maybe you were a family member, concerned that in an unsafe situation, I would not be able to call for help.
There are four layers of reasoning beyond my refusal to have a cellphone, despite being an active Internet user. In order of least to greatest importance:
First, mobile electronics are uncomfortable to me. My time on computers is largely spent on writing, programming, and art; for me these tasks require full-sized keyboards or drawing tablets. This is not an ethical reason to avoid phones and tablets, of course, and I recognise that many people have uses more suited to the tiny form-factor.
Second, cellphones users create cellphone culture. In a fraction of an adult lifetime, cellphones have changed from nonexistent to socially acceptable to use while talking to someone in real-life. This culture is not inevitable for digital electronics – many people use technology responsibly, for which I applaud them – but it remains depressingly common. If I were to have a phone in front of my nose while pretending to talk to my own friends, it would continue to perpetuate the notion that this is okay behaviour. As I fear I might become someone who misuses technology in this way, I avoid carrying a cellphone at all to avoid the ethical risk.
Third, cellphones are grave risks to freedom and privacy. The vast majority of phones on the market run proprietary operating systems, like iOS, and are chock full of proprietary software. Additionally, unlike most laptops and desktops, many of these operating systems run signature checks. That is, it is cryptographically impossible and in some cases illegal to replace the system with free software. This in and of itself is a reason to refuse to touch these devices.
The real situation is unfortunately worse. In conventional electronics, there is a single main chip inside, the CPU. The CPU runs the operating system, like GNU/Linux, and is in full control of the machine. It is not this way for cellphones; these devices have two main chips – the CPU and the baseband. The former has the usual set of freedom issues; the latter is an Internet-connected blackbox with a terrifying set of capabilities. At minimum, due to the design of the cellphone networks, any time that the phone is connected to the network (that is, the baseband is online), the user’s location can be tracked by triangulating cell towers. Already the risk is unacceptable for many people. Traditional telephony operations are vulnerable to surveillance and tampering, as neither calls nor texts are encrypted. And, to add insult to injury, few phones feature acceptable baseband isolation. That is, the CPU, which might run free software, does not control the baseband, which for practical purposes is illegal to run free software in the United States. Rather, in many cases, the baseband controls the CPU. It doesn’t matter if encrypted messaging over XMPP is used if the baseband can simply take a screenshot without the CPU-side operating system’s knowledge nor consent. Alternatively, again depending how the baseband is connected to the rest of the system, it may have the capabilities to remotely activate the microphone and camera. 33 years late, a world in which everyone carries a cellphone surpasses George Orwell’s nightmares. Maybe you have “nothing to hide”, but I for one still care about my privacy. Cellphones are spooky. Count me out.
Finally, in light of the grave implications for society and freedom, I refuse to perpetuate this system. I could decide to carry a cellphone anyway, deciding that as a boring person I can sacrifice the freedom in the name of instantly-gratifying convenience. But by being complacent, I would only add one to the size of the problem, a heavy ethical burden when using the cellphone network contributes to the network effect, as the name suggests.
If I were to have my phone out in front of others, I would be signaling that “cellphones are okay”. If anybody looks up to me ethically, they too might continue to use a cellphone.
If I allowed my friends to text me rather than use more ethical media, I would be signaling that “texting is okay” and “it is reasonable to expect people to text”. If they were on the fence about the ethics and need of carrying a phone, this might push them to keep it.
If I used a phone for activities in class, I would be signaling that “21st century students should have a phone”. I would rather be the final holdout in the class to remind them that this is not an ethical assumption.
If I get a puzzled look from my acquaintances, confidants, and teachers, I now have the opportunity to educate them about free software and privacy. Few people are aware of the risks of these “portable surveillance devices” as Richard Stallman would write. These “awkward moments” are perfect opportunities to help them make a more informed decision.
By carrying a cellphone I would be perpetuating something evil. By actively refusing to carry one, I push back and actively do something good.
So, rather than use a cellphone, what are my alternatives?
For most digital tasks, including writing this post, I use a laptop running free software. As a bonus, to connect to the Internet, I use a Wi-Fi card which runs free firmware!
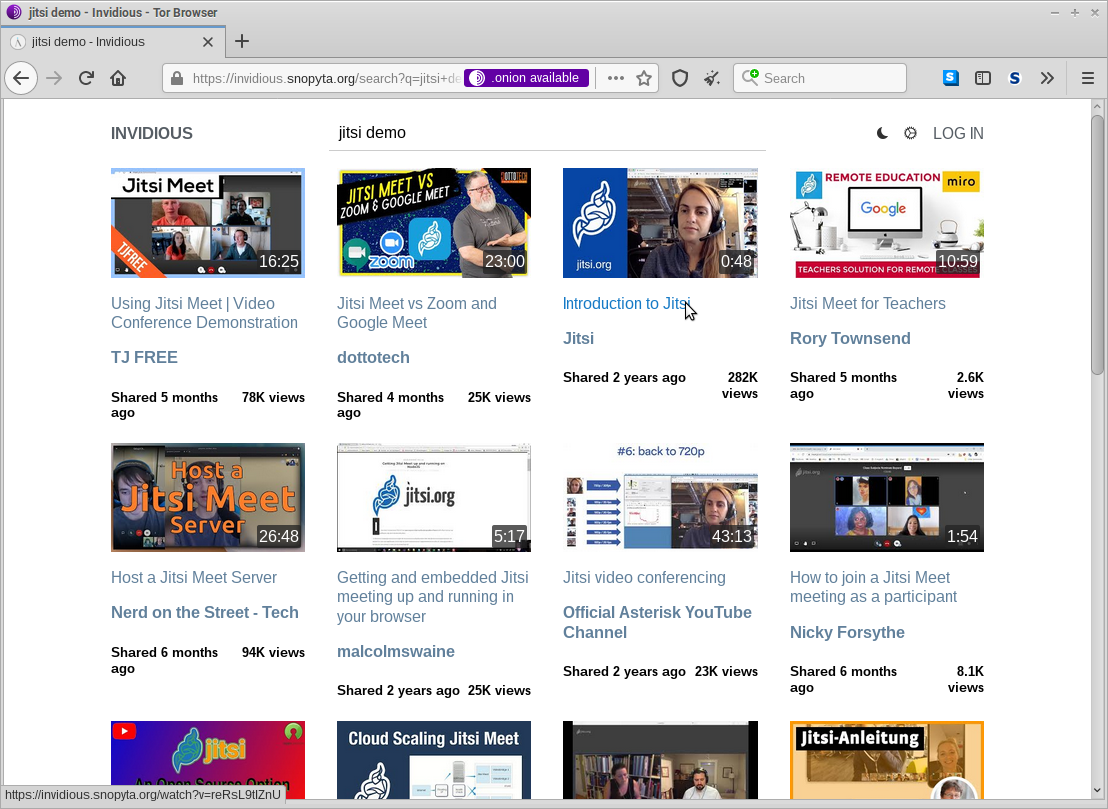
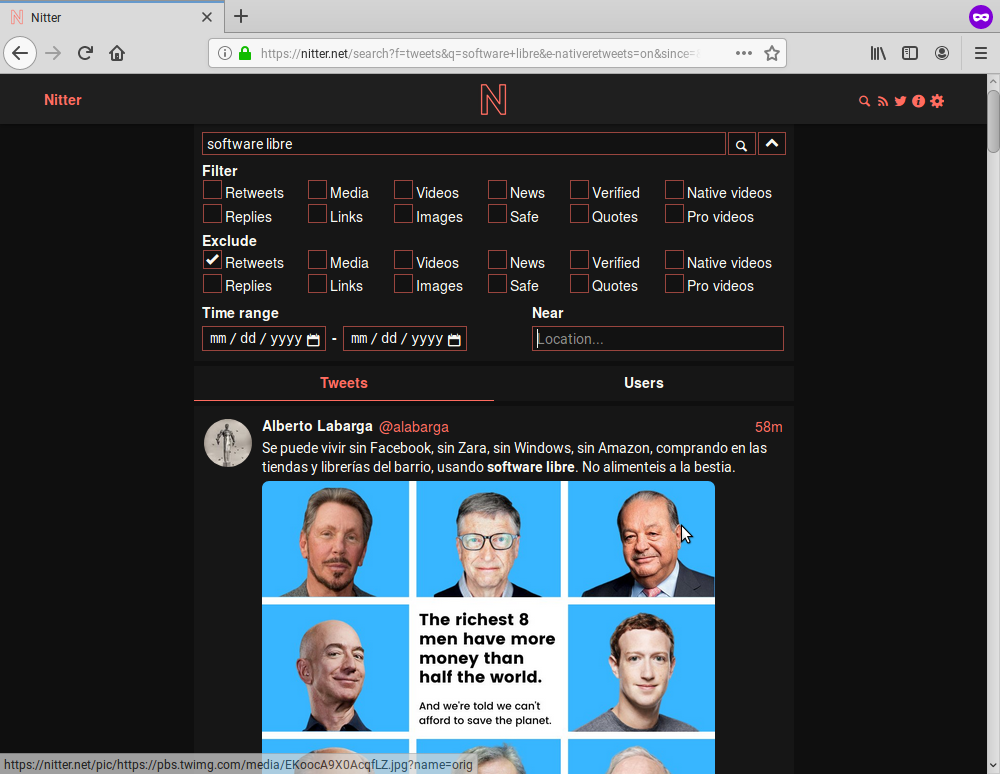
To talk to my friends, I use decentralised, open specification protocols where possible. In particular, I’m available on email, XMPP, and Mastodon. In some cases where this is not possible due to the network effect, I use free centralised systems like IRC. Occasionally, I use proprietary systems that have been reverse-engineered for use with free software, like Discord [the reverse-engineering project she linked to no longer exists]. Where possible, I layer on strong encryption implemented with free software, like GPG and OTR, for extra protection against privacy threats. If locational privacy is an issue, I will connect via Tor. Any one of these measures is a major step above phone calls, text messaging, Whatsapp, or Snapchat. All of them together will shield you from most adversaries.
To connect while I am away from home, I look for public Wi-Fi networks, which can be made secure when paired with encryption and Tor. If this is not an option, I may need to ask someone else to borrow their electronics – this is unfortunate, but while the network effect is in play, it is ethically acceptable to exploit it. Most of the time I will avoid connecting to the Internet away from home anyway; I’m more productive offline!
So, yes, I do get by without a cellphone. It is not always convenient, but productivity, freedom, and ethical behaviour win over convenience any day.
I encourage you to do the same.